In today’s fast-paced digital world, cybersecurity is a top priority for businesses of all sizes. As technology continues to evolve, so do the threats that compromise data integrity and business operations. TMD Technology Services understands the importance of safeguarding digital assets. Here are some essential computer security recommendations to keep your systems secure.
1. Implement Strong Authentication Methods
Multi-factor authentication (MFA) adds an extra layer of security beyond just usernames and passwords. Implementing MFA ensures that even if credentials are compromised, unauthorized access is still prevented. Additionally, consider adopting passkeys as a modern, password-less authentication method to enhance security and reduce the risk of credential theft.
2. Keep Software and Systems Up to Date
Outdated software is a prime target for cyberattacks. Regularly updating operating systems, applications, and antivirus software helps protect against vulnerabilities. Automated update scheduling can simplify this process.
3. Educate Your Team on Cybersecurity
Human error remains one of the most significant security risks. Conduct regular training sessions to educate employees about recognizing phishing emails, using strong passwords, and following best practices for data protection. Implement phishing tests to assess employee awareness and identify areas for improvement, helping to build a proactive security culture.
4. Back Up Data Regularly
Frequent data backups minimize downtime in the event of a ransomware attack or system failure. Employ both on-site and cloud-based solutions to secure critical information. Additionally, consider cloud-to-cloud backup solutions for services like Microsoft 365 and Google Workspace to ensure continuous data availability and protection against data loss.
5. Utilize Network Segmentation
Implementing DNS protection can further secure network boundaries by blocking access to malicious websites and preventing data exfiltration. Integrating DNS protection into your cybersecurity strategy helps reduce the risk of phishing and malware attacks.
Segmenting your network reduces the risk of lateral movement by attackers. Separating sensitive data from other parts of the network creates isolated environments that are harder to infiltrate.
6. Monitor and Respond to Threats in Real-Time
Invest in advanced monitoring tools that detect unusual activities. A robust incident response plan will help mitigate damage during a security breach.
Utilizing advanced threat detection tools like SentinelOne can significantly enhance real-time monitoring capabilities. SentinelOne’s AI-driven endpoint protection continuously scans for suspicious activities, providing rapid response and containment.
Final Thoughts
Proactively managing computer security is essential for staying ahead of evolving cyber threats. TMD Technology Services can leverage these recommendations to enhance client protection and maintain trust in today’s competitive tech landscape. Contact us to learn how we can help implement these strategies for your business.




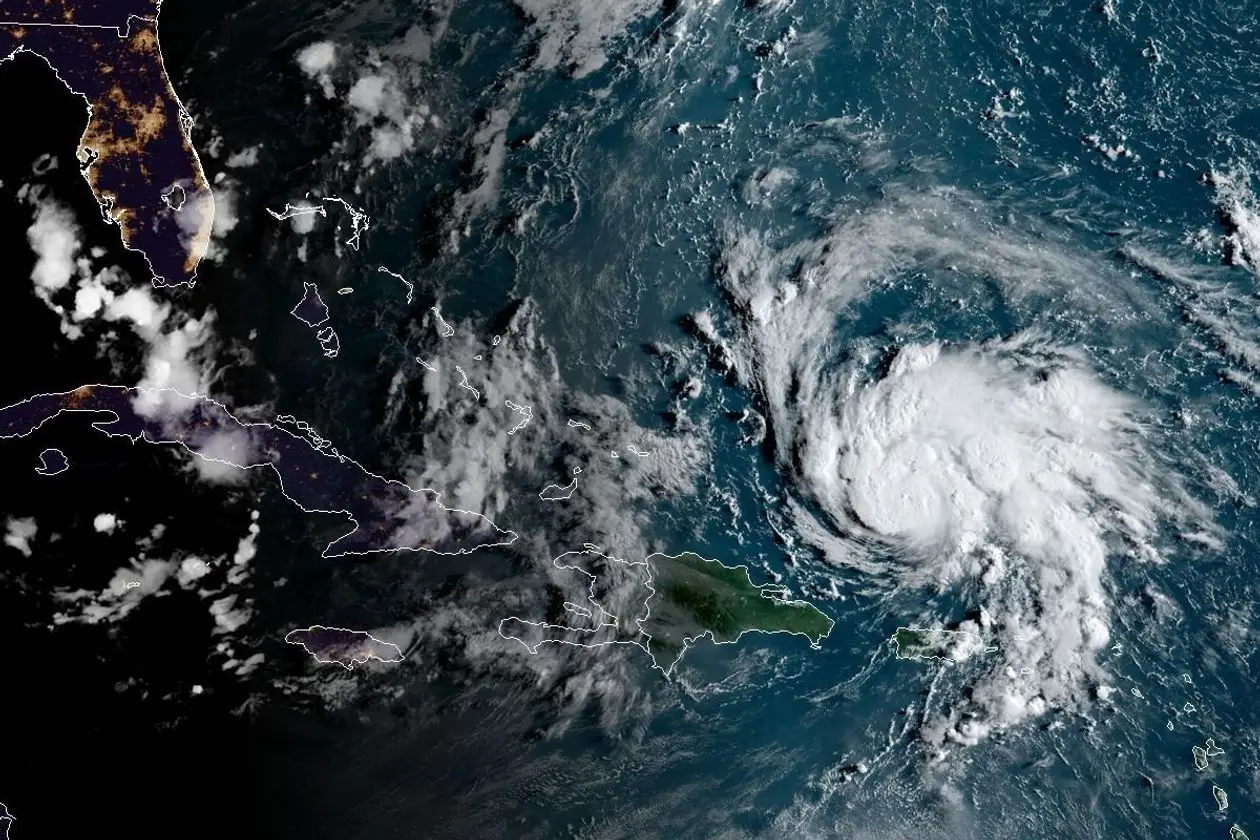

 Hurricane Office Protection Suggestions include some of the following based on severity.
Hurricane Office Protection Suggestions include some of the following based on severity.